Do you recognise these logos?
.png?width=1920&name=Untitled%20design%20(24).png)
I know what you're thinking.
What do they mean? Do I want them? How do I get them?
Please don't think downloading the image from Google and uploading it to your website will suffice. You'd end up in A LOT of trouble.
Understandably, you're still determining if these logos are relevant to your organisation.
It doesn't mean they're valuable because they're everywhere, right?
Wrong. These little Cyber Essentials logos could be the difference between the success or decline of your organisation.
Why is that? Let's start with the fundamentals of Cyber Essentials.
What is Cyber Essentials?
The National Cyber Security Centre (Part of GCHQ) created Cyber Essentials to help organisations protect themselves against common cyber security threats.
In essence, the UK Government are trying to help your organisation become safer and more secure. The government wants fewer breaches, fewer attacks and ultimately, less private data becoming public.
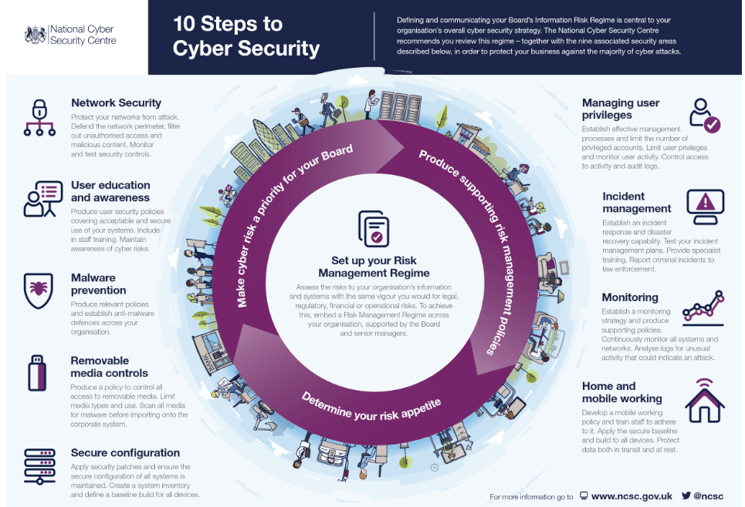
This is why the government created the '10 Steps to Cyber Security' scheme (which you can see below), and this scheme formed the foundation of the Cyber Essentials scheme.
Cyber Essentials implements five technical controls to help your organisation reduce the cyber threat by 80%.
Yes, you are reading that correctly; it isn't a typo.
Cyber Essentials will guarantee your organisation a cyber threat reduction of 80%.
So what are these five technical controls and what do they do?
- Firewalls and Internet Gateways - Cyber Essentials certification requires that you configure and use a firewall to protect all your devices, particularly those that connect to public or other suspicious and unreliable Wi-Fi networks.
- Secure Configuration - Cyber Essentials certification requires your organisation to only use software, accounts and apps that are frequently used. The key here is that they must be necessary to your organisation.
- Access Control - Cyber Essentials certification requires that you control access to your data through user accounts. Also, administration privileges are only given to those that need and furthermore, the use of the data with those accounts is controlled.
- Malware Protection - Cyber Essentials certification requires that you do at least one of the following to defend against malware: Whitelisting, Sandboxing or Installing anti-malware software.
- Patch Management - Cyber Essentials certification requires that you keep your devices, software and apps up to date.
Reducing cyber risk by 80% is already a significant benefit of Cyber Essentials, but why else have so many organisations decided to become Cyber Essentials certified?
Why become Cyber Essentials certified?
As you know, cybercriminals want your data. The skill level of a cybercriminal can vary, but when it comes to SMEs (Small and Medium Enterprises), even the most basic cybercriminal can hack into your systems IF you lack the correct measures.
The guys over at Business Matters Magazine have done a great job conveying the importance of cyber security to SMEs, and it is worth checking out after you're finished here!
With the five controls I've mentioned above being fully implemented at your organisation, you'll have prevented many competent cyber criminals from gaining access to your data and reduced the overall threat by 80%.

What can Cyber Essentials do for your organisation?
So why else would someone want these logos on their website? To understand this on a deeper level, we need to dive into the benefits of Cyber Essentials, which can bring value to your organisation in different ways.
I've already mentioned the 80% reduction in cyber threats, but another significant benefit of Cyber Essentials is enhancing your reputation.
Customers and clients will come onto your website, see the logo, and know their data is safe. They will have more respect for you because you showed respect for their data.
Cyber Essentials can also help you land those government contracts you've always hoped for.
This is a goal for many ambitious organisations, but legally you need to be Cyber Essentials certified. It is a requirement to be able to bid for and land a government contract.
To further understand the advantages, check out 10 surprising benefits of Cyber Essentials.
The Cyber Essentials Process
Now that you understand what the logos mean, let's talk about how you can get those logos onto your own organisation's website.
Getting the Cyber Essentials logos on your website is a four-step process:
1. Choose a Certification Body
Certifying bodies can assess and certify organisations for Cyber Essentials and operate under an Accreditation Body.
Since April 2020, IASME (Information Assurance for Small and Medium Enterprises Consortium) has been the sole Accreditation Body and partner of the NCSC, with Certification Bodies working on their behalf across the country to deliver the Cyber Essentials scheme.
Before this, there were five Accreditation Bodies, but the government decided to streamline the process with only one - making it more straightforward for certifying businesses.
Cyber Tec Security are an example of a Certification Body as we can certify an organisation for Cyber Essentials, and we're aligned with IASME.
Choosing a Certification Body will depend on the kind of experience you want. While all can grant you the Cyber Essentials certification, pricing and packaging could differ, and the certification delivery will vary from business to business.
My advice? Ask yourself what you want and do your research!
2. Meet the Cyber Essentials standard
To be able to meet the Cyber Essentials standard, your IT infrastructure needs to meet the requirements to be able to begin the technical process. You can view the requirements for IT infrastructure here.
3. Pass Cyber Essentials
With the guidance of your Certification Body, you can tick off every aspect of each technical control. I'm being literal, too; there is a self-assessment questionnaire that you'll need to tick off as you go along.
The Certification Body will review the responses and determine whether you've met the standard.
You will be awarded Cyber Essentials certification if you have met the standard. (And congratulations will be in order!).
4. Use The Cyber Essentials Logo
Now you've done the hard part; all you need to do is show that you are Cyber Essentials certified!
You can use the logo on the following:
- Websites
- Promotional Material
- Letter Heads
- Email Signatures
This is how you become Cyber Essentials certified, and if you are interested in gaining the Cyber Essentials Plus logo, the process is different, and there are a few other things you'd need to know.
To learn more about Cyber Essentials, check out our Ultimate Guide to Cyber Essentials which will tell you everything you need to know about Cyber Essentials for FREE.
Download the Free eBook



