The tragic events in Ukraine that have been dominating our news outlets over the last few weeks have had implications in numerous areas, including business, the economy and security. While Ukraine has been defending their country from the Russian offensive on the ground, a different kind of battle has been happening in the cyber space.
Cyber Attacks on Ukraine
As Russia was gathering their troops around Ukraine’s borders back in January, Ukraine was hit by a major cyber attack, seemingly targeted at their government, with around 70 key websites taken offline.
The hackers replaced text on many of the websites to read ‘be afraid and wait for the worst’. Although Russia denied allegations made that they were responsible for the cyber attacks, it was widely felt that this statement may be seen as a warning in the lead up to Russia’s invasion.
Microsoft then investigated the attack further, explaining that malware, though designed to look like ransomware, was purely destructive, and had the potential to render certain government infrastructure inoperable.
Fast forward to just a few weeks later, and Ukraine was yet again a target. What is being described as the biggest of its kind in Ukraine’s history, the major DDoS attack disrupted the websites of both the defence ministry and army, as well as those of the country’s two largest banks. Distributed Denial of Service attacks are designed to overload a website with requests, forcing it to crash.
All signs suggested Russia, who had at this stage amassed around 150,000 soldiers at the Northern, Eastern and Southern borders, was to blame. The Head of the Ukrainian Intelligence Agency’s Cyber Security Department, Ilya Vityuk, also pointed out that this powerful attack was likely to have cost millions of dollars, making it unlikely that an individual or hacking group would be responsible.
Most recently, a third DDoS attack was identified on hundreds of systems across Ukraine. In addition, data wiping malware, later dubbed HermeticWiper, was spotted, with a timestamp that could even trace it back to December 28th, suggesting the attack had been in planning for at least a few months.
How is Ukraine Responding?
Russia is no stranger to cyber crime, and has been blamed for several attacks on Ukraine since 2014. Cyber measures can be a powerful tool to utilise during war if only to arouse panic, wear down morale and keep people guessing.
Ukraine is getting better at protecting itself from these kinds of incidents, however, and other countries have flocked to support them in their time of need. NATO has condemned the attacks, and offered Ukraine access to their malware information sharing platform, to aid their defences. A cyber rapid response team (CRRT) has also been deployed across Europe, made up of experts committed to helping Ukraine protect against cyber attacks.
Australia too has responded, offering cyber security support to Ukraine by way of bilateral Cyber Policy Dialogue that will allow for discussions on cyber threats, policies and strategies. They also plan to provide cyber security training for Ukrainian officials.
Do These Risks Extend Beyond Ukraine?
The biggest question for cyber security experts in the West and in the US is: Are we likely to see an influx of cyber attacks as allies to Ukraine?
This certainly is a possibility given Russia’s track record, for example, during 2017, NotPetya ended up affecting organisations worldwide. The onslaught of attacks on Ukraine has therefore led both the UK and US to encourage organisations to bolster their defences and be prepared for the worst. There have already been some spillover attacks, with wiper malware detected in Ukraine also affecting Ukrainian government contractors in Latvia and Lithuania.
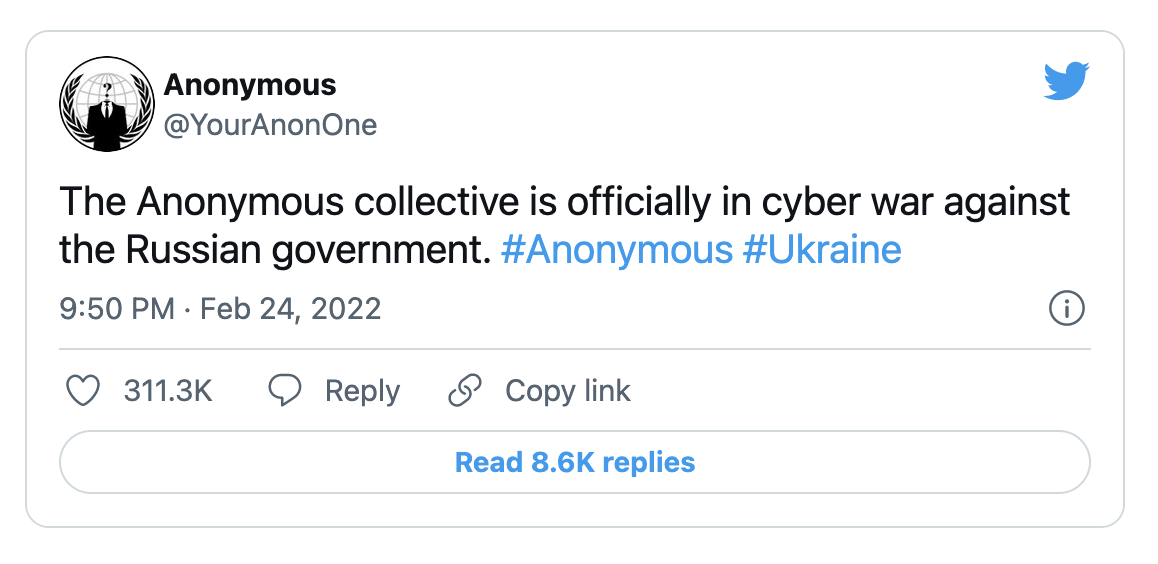
And it is not only government-sanctioned cyber warfare that could present risk. Many well known cyber crime groups seem to have taken sides during the Russia-Ukrainian crisis, for example, the Conti ransomware group, who have rallied behind the Russian government, threatening ‘retaliatory measures in case the Western warmongers’. Hacker collective, Anonymous, has pledged their allegiance to Ukraine and have, in recent days, launched attacks that took down many Russian government sites and state-backed news outlets.
What Can Organisations Do to Stay Secure?
Of course, it’s always best practice to assume you’re going to be attacked as this is going to guarantee the most effective defences, but pleas for stronger security have amplified in recent weeks with the increased possibility of attack from Russian and allied forces.
“While we are unaware of any specific cyber threats to UK organisations in relation to events in Ukraine, we are monitoring the situation closely and it is vital that organisations follow the guidance to ensure they are resilient.
Over several years, we have observed a pattern of malicious Russian behaviour in cyberspace. Last week’s incidents in Ukraine bear the hallmarks of similar Russian activity we have observed before.”
- Paul Chichester, NCSC Director of Operations
If cyber security is not usually a priority for your business, it should be in times of crisis. Here are 6 ways you can strengthen your defences and be prepared for cyber attack.
1. Check devices and software is all up to date
Make sure all systems used by your organisation have the latest security updates to protect against known security vulnerabilities. There should be no end-of-life software present or active. Where possible, switch on automatic updates.
2. Review access controls
Check what user accounts can access what data and ensure that multi-factor authentication and strong passwords are in place for added protection. Be particularly careful with accounts that have access privileges for things like handling administrative tasks or accessing sensitive data.
3. Have an incident response plan
Revisit or create policies to prepare your business for dealing with a cyber incident. The response plan should detail logistics including communication that needs to happen, who the primary decision maker will be, and what should happen should a situation escalate.
4. Review your data backups
Test your backup solutions and make sure you can restore data quickly and easily should you need to. You should also have a recent offline copy of your backups. These backups can be critical in a crisis situation, especially with the recent wiper attacks, which can wipe all your data if you refused the ransom.
5. Check firewalls are working properly
Make sure your firewall rules are as expected. B2B VPN connections are a particular concern if they lack firewalls, so it is advisable to review these and ensure you're blocking at least the known dangerous protocols to avoid leaving an entry point open to hackers.
6. Keep your workforce aware
Help your employees understand the current heightened risks and stress the role they have to play in your organisation's security. This will help get buy-in from higher up as well as encourage staff to be more cyber vigilant as they go about their day, particularly around things like phishing and misinformation campaigns, and ensure they are equipped with the right guidance around spotting and reporting threats.
As you can see, the most important thing that businesses can do is make sure they have the fundamentals in place and have a general increased awareness of cyber threats within their organisation. While you may not be a target as such, it is very possible, as we've seen before, that other organisations get caught up in attacks as collateral damage, so it is important to do what you can to stay protected.
For more cyber security advice, particularly in light of current events, reach out to us at contact@cybertecsecurity.com or 0117 497 3331 and one of our specialists will be happy to guide your organisation.

